Divide and Don’t Get Conquered
I was recently asked to contribute to a network redesign project, at first I was just asked to contribute, then I was tasked with creating the plan, and was then given a directive to implement it.. I thought that was quite exciting as I wasn’t overly familiar with their network vendor brand and I enjoy getting my hands dirty. I prayed about it and asked God for wisdom, I don’t want to rely on myself – I want God to be the power I rely on and get the glory in my life. So anything I’ve accomplished, the glory belongs to him alone.
Sometimes you have have a single large building with multiple individual businesses that share the internet but want to keep the traffic from each network completely separated from each other, they will also usually have some centralized devices that are shared – in that case, you want to allow traffic flow into that centralized area but only allow traffic to flow back to the source of the request. Think of it like you can call a number, and they can answer and talk to you but they can only receive calls – they can’t make calls.
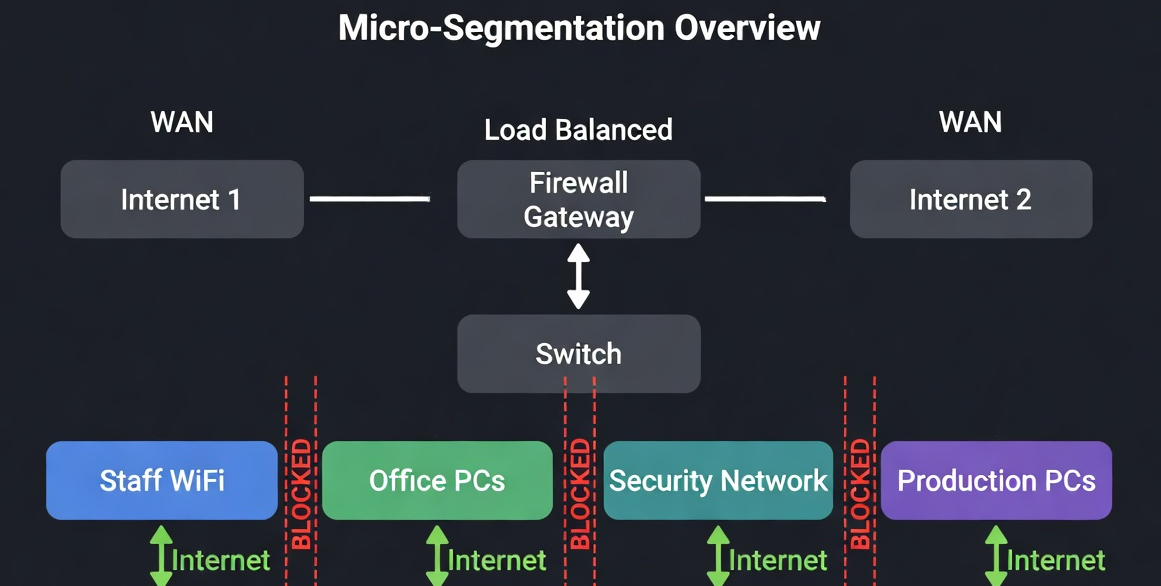
In this multi-tenant type of situation – bigger can mean better, say you have 3 businesses and they line up with the situation above, they can buy 3 cheap routers & 3 switches & 3 internet connections, 3 patch panels, and 3 subpar copiers.. sure, they would be segmented but they would also be spending the most amount of money for the least amount of gain. They could pool together and buy a capable router, higher end switch say a Unifi switch, a copier with a repair contract, and pay for 2 internet connections that are load balanced with fail-over. They would pay less money, have much better equipment and security while maintaining all the benefits of being physically segmented.
Other times you have a single large business but you have multiple departments that don’t really need to talk to each other (from a network traffic perspective) – that is another great candidate for segmentation.
The aim behind the redesign is microsegmentation. What that means is separating a network into distinct segments based on categorization of department or function, and then apply security policies or complete isolation to the network.
Many networks start small as a flat network in a single subnet, over time devices get added and the network grows; more traffic is generated, and every device can see and talk too every other device – this is called being in the same broadcast domain.
If one station gets infected or has ransomware – it may try to entangle all other stations within its reach but with microsegmentation, traffic isn’t able to jump across hard network boundaries – as they are limited to their respective broadcast domain.
There are a couple of other considerations to keep in mind, if you are on a single flat network, all your management interfaces are likely reachable from the default network… aka, anyone who plugs into a network port or even your main WIFI network can reach and possibly breach the administrative controls of your network.
The management network should be on it’s own network segment and not accessible from WIFI – I also disable all interfaces that are not in use.
You may also have a MFP copier or other shared device that need to accept network traffic from all segments; segments that are otherwise isolated… so you can allow some traffic to cross the boundaries in a stateful manner so that the source initiates the traffic and the firewall checks its connection table and allows established traffic to return. It’s also perhaps a good idea to have some of your networks pass Multicast DNS to allow for discovery.
The reason behind all these good practices are limiting your attack surface and eliminating unsafe points from your network. A network that has nothing of these things in mind can be hacked in the blink of an eye really. I’ve seen some good networks hit with mind blowing hacks – as a defender – you have to get it right all the time, as an adversary – they only have to get it right once.
It’s a good idea to look at your network from an outsiders perspective and think about what you can improve and tweak.
Have a great week!
Jason
